GRAVICOM has over 22 years experience in DoD Information Assurance programs. GRAVICOM can help your team implement a robust IA program, including:
- Perform oversight of the development, implementation and evaluation of an organizational information system security policy
- Perform analysis of network security, based upon the DCID 6/3, DITSCAP, DIACAP, DIARMF, and NISPOM Chapter 8 certification and accreditation process
- Advise customers on IT certification and accreditation issues
- Create/update/maintain POA&Ms and security controls
- Execute/update/maintain STIG checklists, Retina scans, validate security posture
- Create/update/maintain technical diagrams, software lists, hardware lists, and C&A plans
- Provide detailed reports of IAVs, including assistance with VMS and mitigation plans
- Provide Navy Validator services
- Provide Marine Corps Validator services
- Enable customers in DoD Information Assurance applications such as Navy eMASS, and XACTA (MCCAST)
- Perform risk assessments and make recommendations to customers
- Advise program managers on security testing methodologies and processes
- Evaluate certification documentation and provide written recommendations for accreditation
- Periodically reviews system security to accommodate changes to policy or technology
- Continuously evaluate IT threats and vulnerabilities to determine whether additional safeguards are needed
- Ensure that certification is accomplished for each information system
- Execute Program Of Record (POR) Independent Verification & Validation (IV&V) with our CNSS-4016 certified risk analysts
- Develop and maintain a formal Information Systems Security Program
- Develop, implement, provide guidance, and enforce security policies and procedures
- Ensure that all Information Assurance Officers (IAOs), network administrators, and other IT personnel receive the necessary technical and security training to carry out their duties
- Develop, review, endorse, and recommend action by the designated approval authority (DAA) of system certification documentation
- Ensure approved procedures are in place for clearing, purging, declassifying, and releasing system memory, media, and output
- Conduct certification tests that include verification that the features and assurances required for each protection mechanism are functional
- Maintain a repository for all system certification/accreditation documentation and modifications (See GRAVICOM’s Repository)
- Coordinate security inspections, observations, tests, interviews, and documentation reviews
- Develop policies and procedures for responding to security incidents, and for investigating and reporting security violations and incidents
- Ensure proper protection or corrective measures have been taken when an incident or vulnerability has been discovered within a system
- Ensure that data ownership and responsibilities are established for each AIS, to include accountability, access rights, and special handling requirements
- Ensure development and implementation of an information security education, training, and awareness program, to include attending, monitoring, and presenting local security training.
- Ensure that security testing and evaluations are completed and documented
- Evaluate threats and vulnerabilities to determine whether additional safeguards are needed
- Assess changes in the system, its environment, and operational needs that could affect the accreditation
- Ensure that certification is accomplished on each IT system
- Periodically review system security & security test plans
- Conduct periodic testing of the security posture of the system
- Ensure configuration management (CM) for security-relevant hardware, software, and firmware are properly documented.
- Ensure that system recovery processes are monitored to ensure that security features and procedures are properly restored
- Ensure all system security-related documentation is current and accessible to properly authorized individuals
- Ensure that system security requirements are addressed during all phases of the system life cycle
- Perform periodic in-house self inspections; identify security discrepancies and report security incidents
- Coordinate all technical security issues outside of area of expertise or responsibility with SSE and ISSE
- Provide expert research and analysis in support of expanding programs and area of responsibility
- Create, Modify, and Execute DIACAP packages through the Certification and Accreditation cycle.
- Complete Checklists, Retina Scans, SCAP Scans, Risk Assessment Reports (RARs)
- Executed DIARMF, DIACAP, and DITSCAP processes, achieved IATT, IATO, and ATOs for many systems
- Provide Senior Navy Validation services
- Provide Information Security Systems Engineering (ISSE) services – Systems Engineering, Programmatic support, Information Assurance support, and Certification & Accreditation expertise.
- Create technical Program level systems engineering documentation including:
- Information Assurance Program Docs, Decisional Briefs, & Technical Diagrams
- Program Protection Plans (PPPs), Acquisition Information Assurance Strategy (AIAS), Cyber Security Strategy (CCS), and Security Risk Assessments (SRAs)
- Memorandums for the Record (MFRs), FISMA compliance Docs
- Privacy Impact Assessments (PIA), Naval Nuclear Propulsion Info (NNPI) checklists,
- Business Case Analysis (BCA) and Business Impact Analysis (BIA)
- Analysis of Alternatives (AoA) and Spiral Acquisition Development Briefs
- Negotiate Entire Program Moves into the Navy Enterprise Data Center (NEDC) on NIPR and SIPR
- Facilitate technical and administrative efforts
- Coordinate IA and technical activities between groups
- Perform C&A activities to get new environments accredited.
- Perform as a Navy Validator for packages in SPAWAR and NAVSEA.
- Negotiate directly with the Navy CA and ODAA on technical & administrative issues.
- Perform as Information Systems Security Engineer (ISSE) for SPAWAR & NAVSEA packages
- Create C&A packages, complete artifacts such as scans, checklists, SCAP benchmarks, mitigations, POA&Ms, RARs, Contingency Plans, Incident Response plans, System Security plans, Scorecards, SIPs, PIAs, Web Risk Assessments (WRAs), eAuthentication Risk Assessments, Test Plans, Implementation Plans, Validation Plans, and other artifacts as needed.
- Serve as a technical liaison between Program Managers & Engineering to facilitate adoption of DoD and Navy policy for STIG implementation, regular automated scanning, FISMA compliance & reporting, DADMS registration, DITPR-DON registration & reporting, JITC Waivers, DON-CIO Escalations, POA&M maintenance & milestone tracking.
- Interface with the configuration management team to institute Engineering Change Requests (ECRs),
- Perform research and implementation of Navy and DoD policy for the proper implementation of information security policies, technologies, and operations.
GRAVICOM is a FULLY QUALIFIED CORPORATE NAVY VALIDATOR Company.
To see a full copy of the Navy Validator list, please see the Navy C&A Web Portal at:
https://www.portal.navy.mil/netwarcom/navycanda/default.aspx (NOTE: Only reachable from NIPRNET)

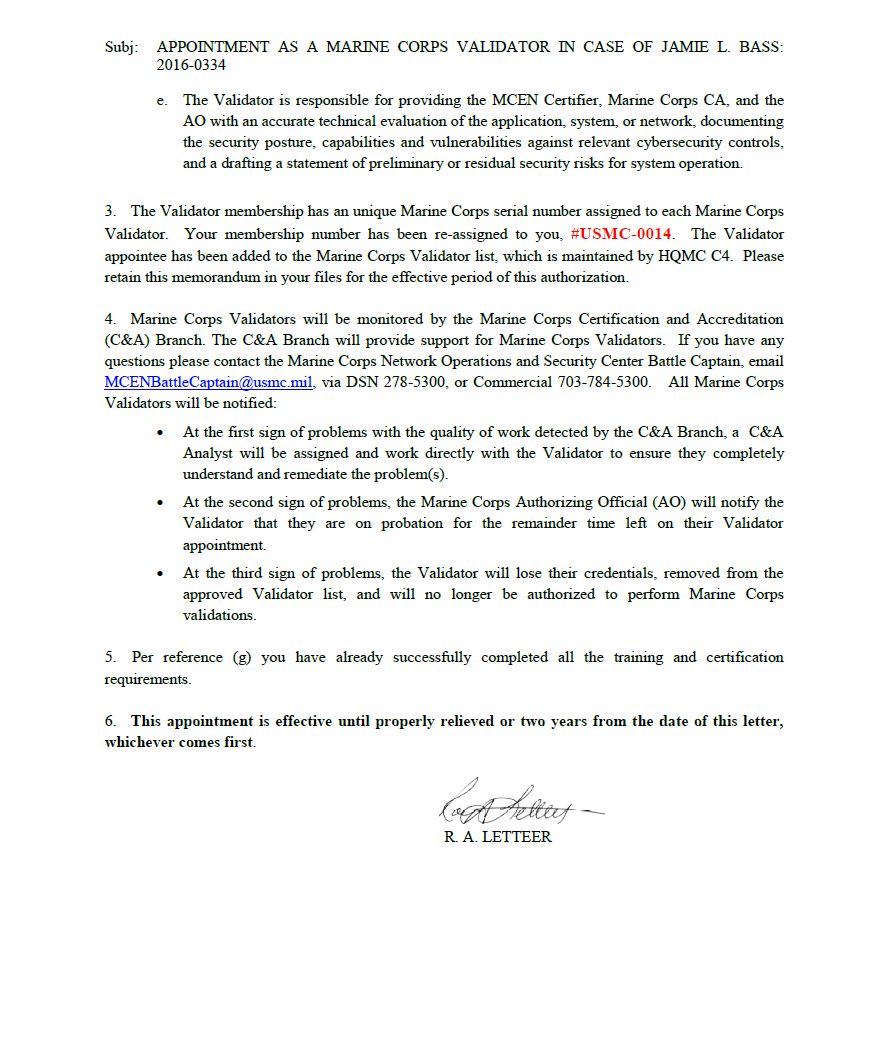
GRAVICOM is a FULLY QUALIFIED CORPORATE USMC VALIDATOR Company.
A full list of USMC Validators can be found here: https://c4.hqi.usmc.mil/CA.asp
(NOTE: URL above is only reachable from NIPRNET)
United States Marine Corps Validation appointment letter for Jamie Bass (USMC Validator MC-0014) is below.
 .
.
.
.
.
.
.
.
.
.
